| ↩︎ | ↖︎ | ↑︎ | ↘︎ | ↪︎ |
Foreign commands for external utilities (and the HTTPD control functionality) will need to be assigned from the adminstration users' LOGIN.COM either explicitly or by calling the WASD_ROOT:[EXAMPLE]WASDVERBS.COM procedure.
Ever had to go to extraordinary lengths to find out exactly what your browser is sending to the server? The server provides a request echo facility. This merely returns the complete request as a plain-text document. This can be used for for checking the request header lines being provided by the browser, and can be valuable in the diagnosis of POSTed forms, etc.
This facility must be enabled through a mapping rule entry.
It may then be used with any request merely by inserting "/echo" at the start of the path, as in the following example.
The hiss facility provides a response stream made up of random alpha-numeric characters (a sort of alpha-numeric white-noise). No response header is generated and the stream will continue (by default) up to one megabyte of output, or until the client closes the connection. This maximum may be controlled my appending an integer representing the number of kilobytes maximum to the mapping. This facility must be enabled through a mapping rule entry and may then be used for specific requests.
Usage details are described in Security Considerations of WASD Configuration).
The stream facility provides a quantified or unlimited response stream of printable or binary octets. It is intended as a light-weight data source delivering content at the maximum throughput capable by the server and platform. This can be used as a test source or for end-to-end metrics. This facility must be enabled through a mapping rule.
It may then be used to generate streams of data with various characteristics and sizes by including parameters in the URL.
Need to locate where VMS has the HTTPd files? This simple facility maps the supplied path then parses it to obtain a resulting VMS file specification. This does not demonstrate whether the path actually exists!
This facility must be enabled through a mapping rule entry.
It may then be used with any request merely by inserting "/where" at the start of the path, as in the following example.
The Xray facility returns a request's complete response, both header and body, as a plain text document. Being able to see the internals of the response header as well as the contents of the body rendered in plain text can often be valuable when developing scripts, etc.
This facility must be enabled through a mapping rule entry.
It may then be used with any request merely by inserting "/xray" at the start of the path, as in the following example.
The Consolidate Access LOGS utility (pronounced similar to the breakfast cereal brand :-) merges multiple HTTP server common and combined format access logs into a single log file with records in time-order. Due to the granularity of HTTP server entry timestamps (one second) the records are sorted to the one second but not within the one second.
It uses RMS and the VMS sort-merge routines to provide the basic consolidation functionality. An RMS search uses the supplied wildcard log file specification. Matching files are opened and each record read. The date/time field is parsed and a binary timestamp generated. Records with formats or date/time fields that do not make sense to the utility are discarded. When all files have been processed the sort-merge is performed using the timestamp as the key. The sorted records are then written to the specified output file.
$ calogs <log-file-spec> [<output-file-name>] [<qualifiers>]
| Parameter | Description |
|---|---|
| /HELP | basic usage information |
| /NOPROXY | discard proxy service records |
| /NOWASD | discard WASD server status/timestamp entries |
| /OUTPUT= | alternate method of specifying merged file name |
| /PROXY | discard non-proxy service records |
| /QUIET | no messages apart from errors |
| /VERBOSE | per-file progress messages |
| /VERSION | display the utility version and copyright message |
Content Security Policy (CSP) is an added layer of security that helps to detect and mitigate certain types of attacks, including Cross Site Scripting (XSS) and data injection attacks.
https://en.wikipedia.org/wiki/Content_Security_Policy
https://developer.mozilla.org/en-US/docs/Web/HTTP/CSP
WASD provides CSP support using mapping rules. See Content Security Policy (CSP) of WASD Configuration.
When POSTed to, this utility appends a timestamp and CSP report JSON to the file specified by the CSPREPORT_FILE logical name. This file must be located somewhere the scripting account has read+write access to. When accessed using a GET the utility accesses the stored CSP reports and returns a formatted HTML report listing each. GET requests (reporting) must be subject to authentication and authorisation.
For further infomation check the descriptive prologue in the WASD_ROOT:[SRC.UTILS]CSPREPORT.C source code.
The HTAdmin utility assists in with the command-line maintenance of $HTA authorization databases. See Authorization Configuration (Basics) of WASD Configuration and 3. Authentication and Authorization.
htadmin <database> [<username>] [<qualifiers>]
| Parameter | Description |
|---|---|
| /ADD | add a new record |
| /CONFIRM | confirm deletion of database |
| /CONTACT="<string>" | contact information for record |
| /CREATE | create a new database |
| /CSV[=TAB|char] | comma-separated listing (optional character) |
| /DATABASE= | database name (or as command-line parameter) |
| /DELETE | delete a database or username record from a database |
| /DISABLED | username record is disabled (cannot be used) |
| /EMAIL="<string>" | email address for record |
| /ENABLED | username record is enabled (can be used) |
| /FULL | listing showing full details |
| /GENERATE | generate a six character password |
| /HELP | basic usage information |
| /[NO]HTTPS | synonym for /SSL |
| /LIST | listing (brief by default, see /FULL and /CSV) |
| /MODIFY | synonym for /UPDATE |
| /NAME="<string>" | full name for username record |
| /OUTPUT= | alternate output for database listing |
| /PASSWORD[=<string>] | username record password (prompts if not supplied) |
| /PIN | generate four-digit "PIN number" for password |
| /[NO]READ | username can/can't read |
| /SORT[=<parameters>] | sort the records into a new/another database |
| /[NO]SSL | user can only authenticate via SSL ("https:") |
| /[NO]WRITE | username can/can't write |
| /UPDATE | update an existing username record |
| /USER=<string> | username |
| /VERSION | display version of HTADMIN |
The /SORT qualifier sorts the current database records according to the /SORT= parameters. It can be used with the /LIST qualifier to produce ordered reports or will output the records into another authentication file. By default it sorts ascending by username. Qualifier parameters allow a sort by DATE or COUNT. Each of these allows the further specification of which date or count; ACCESS, CHANGE or FAILURE.
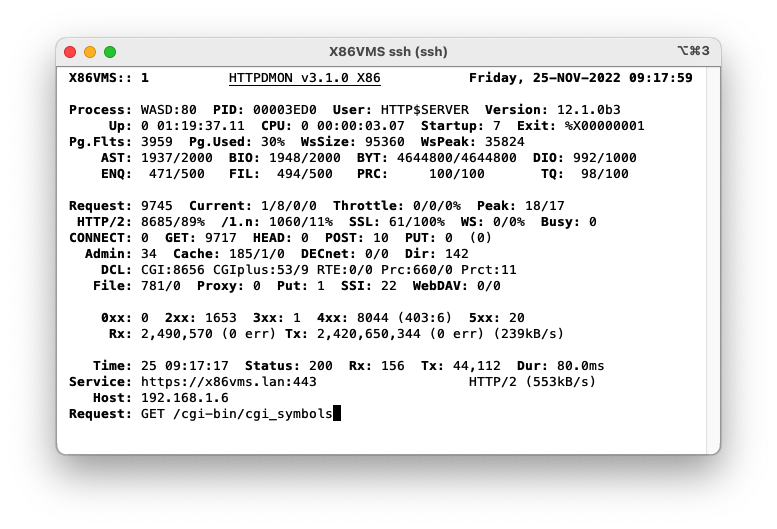
The HTTP server may be monitored in real-time using the HTTPDMON utility.
This utility continuously displays a screen of information comprising four or five of the following sections:
The "/HELP" qualifier provides a brief usage summary.
The server counter values are carried over when a server (re)starts (provided the system has stayed up). To reset the counters use the online Server Administration facility (9. Server Administration).
If [DNSlookup] is disabled for the HTTP server the HTTPDMON utility attempts to resolve the literal address into a host name. This may be disabled using the /NORESOLVE qualifier.
From RFC1321 …
" The [MD5] algorithm takes as input a message of arbitrary length and produces as output a 128-bit "fingerprint" or "message digest" of the input. It is conjectured that it is computationally infeasible to produce two messages having the same message digest, or to produce any message having a given prespecified target message digest. "
The MD5DIGEST utility is primarily provided with WASD for verifying kits as unchanged from the originals released. With the proliferation of mirror sites and other distribution resources it has become good practice to ensure kits remain unchanged from release, to distribution, to installation site (changes due to to data corruption or malicious intent - as remote a possibility as that may seem). Of course it may also be used for any other purpose where the MD5 hash is useful.
For verifying the contents of a WASD release connect to the original WASD distribution site, refer to the download page, and make a comparison between the release MD5 hash found against the list of all archive hashes and the MD5 hash of your archive. That can be done as follows
Of course, if you have not yet installed your first WASD distribution using the MD5DIGEST utility that is part of it is not feasable. The original site can provide kits and pre-built executables for this purpose.
Quick-and-Dirty LOG STATisticS is a utility to extract
very elementary statistics from Web server common/combined format log files.
It is intended for those moments when we think "I wonder how many times
that new archive has been downloaded?", "How much data was transfered
during November?", "How often is such-and-such a client
using the authenticated so-and-so service?", "How much has
the mail service been used?" … and want the results in a matter of
seconds (or at least a few tens of seconds ;-) It is available at the
command-line and as a CGI script.
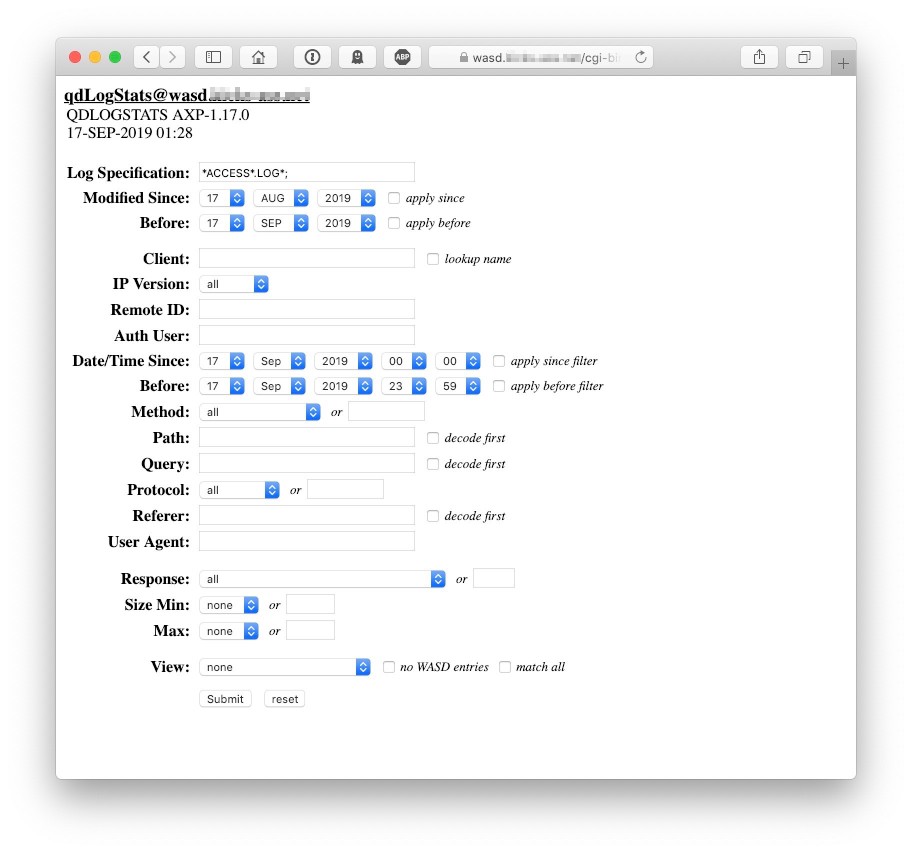
For QDLOGSTATS to be available as a CGI script it must have authorization enabled against it (to prevent potential ad hoc browsing of a site's logs). The following provides some indication of this configuration, although of course it requires tailoring for any given site.
It could then be accessed using
The initial access provides a form allowing the various filters and other behaviours to be selected. The CGI form basically parallels the command-line behaviour described below.
A number of filters allow subsets of the log contents to be selected. These filters support the same string matching expressions as the server (see String Matching of WASD Configuration).
A knowlege of the format and contents of the common and combined log formats will assist in deciding which and to what purpose filters should be used. Record filtering is done in the same order as is finally displayed, so method would be processed before user-agent for instance. Normally a record match terminates on the first non-matched filter (to expedite processing). To compare and report each filter for every record apply the /ALL qualifier. To view records as they are processed use the /VIEW qualifier. This by default displays all matched records, but the optional =ALL or =NOMATCH parameters will display all records, or all those but the matches.
QDLOGSTATS log-file-spec [pattern qualifiers] [other qualifiers]
| Parameter | Description |
|---|---|
| /ALL | compare and report on all supplied filters |
| /AUTHUSER= | pattern (any authenticated username) |
| /BEFORE= | log files before this VMS date/time |
| /CLIENT= | pattern (client host name or IP address) |
| /DATETIME= | pattern ("11/Jun/1999:14:08:49 +0930") |
| /DECODE[=keyword] | URL-decode PATH, QUERY, REFERER before match |
| /METHOD= | pattern (HTTP "GET", "POST", etc.) |
| /OUTPUT= | file specification |
| /PATH= | pattern (URL path component only) |
| /PROGRESS | show progress during processing; a "+" for each file started, a "." for each 1000 records processed |
| /QUERY= | pattern (URL query component only) |
| /REFERER= | pattern (HTTP "Referer:" field, COMBINED only) |
| /REMOTEID= | pattern (RFC819 file) |
| /RESPONSE= | pattern (HTTP response code) |
| /SINCE= | log files after this VMS date/time |
| /SIZE[=keyword] | response size (in bytes) MIN=integer MAX=integer |
| /USERAGENT= | pattern (HTTP "User-Agent:" field, COMBINED only) |
| /VIEW[=type] | display matching log records (ALL, NOMATCH, MATCH) |
The SECHAN utility (pronounced "session") is used by [INSTALL]SECURE.COM and associated procedures to make file system security settings. It is also available for direct use by the site administrator. See Security Considerations of WASD Configuration).
This simple procedure used the FDL facility to convert files to STREAM_LF format. The WASD HTTPd server access STREAM_LF files in block/IO-mode, far more efficiently that the record-mode required by variable-record format files.
NOTE: The server can also be configured to automatically convert any VARIABLE record format files it encounters to STREAM_LF.
WAStee is a utility to generate time-stamped log files containing intervals of a long-lived WASD server process, and/or to consolidate all process log files generated during the defined period. It is the tee in a PIPE sequence.
This utility is UNSUITABLE for sites using multiple instances and/or environments on a node. Only the first of multiple server processes will have the log teed.
For further information check the descriptive prologue in the WASD_ROOT:[SRC.UTILS]WASTEE.C source code.
Grouped here due to similiar intent as WASTEE, create interim snapshots of a long-lived WASD server process, a daily archive from the server process PPF log.
The daily log file is placed in the same location as the server log files. The non-multiple instance log name is <node-name>_yyyymmdd_DAILY.LOG The multiple instance log name is <node-name>_<integer>_yyyymmdd_DAILY.LOG
The daily log file has a timestamp added at startup and then each hour to provide an indication that it continues to run in the absence of any additional server log records.
Enable by logical name WASD_SERVER_DAILY being defined at server startup.
The "WASD Over-The-Shoulder Uptime Picket" is designed to monitor WASD in a production environment for the purpose of alerting operations staff to conditions which might cause that production to be adversely impacted.
Alert triggers include:
Alert reports can be delivered via any combination of:
The utility runs in a detached process and monitors the server environment by periodically polling various server data at a default interval is 15 seconds. As the utility requires access to global memory accounting a per-system WOTSUP is required for each node to be monitored.
The following (somewhat contrived) example illustrates the format and content of a WOTSUP report delivered via OPCOM. Reports delivered via other mechanisms have the same content and similar format.
For further information check the descriptive prologue in the WASD_ROOT:[SRC.UTILS]WOTSUP.C source code.
| ↩︎ | ↖︎ | ↑︎ | ↘︎ | ↪︎ |